Defence & secure deployments
Secure, deployable modular data centres for mission-critical operations
Modular Data System is an engineered modular data centre configuration for defence, government and secure comms—built for rapid deployment, hardening options, and clear technical documentation for procurement.
Designed for security, resilience, and speed
Select the hardening and security level you need—then deploy fast with a configuration that’s ready for review by operators, consultants, and procurement.

Security-first architecture
Layered physical and logical security options, from access control and CCTV integration to secure network zoning and monitoring-ready layouts.
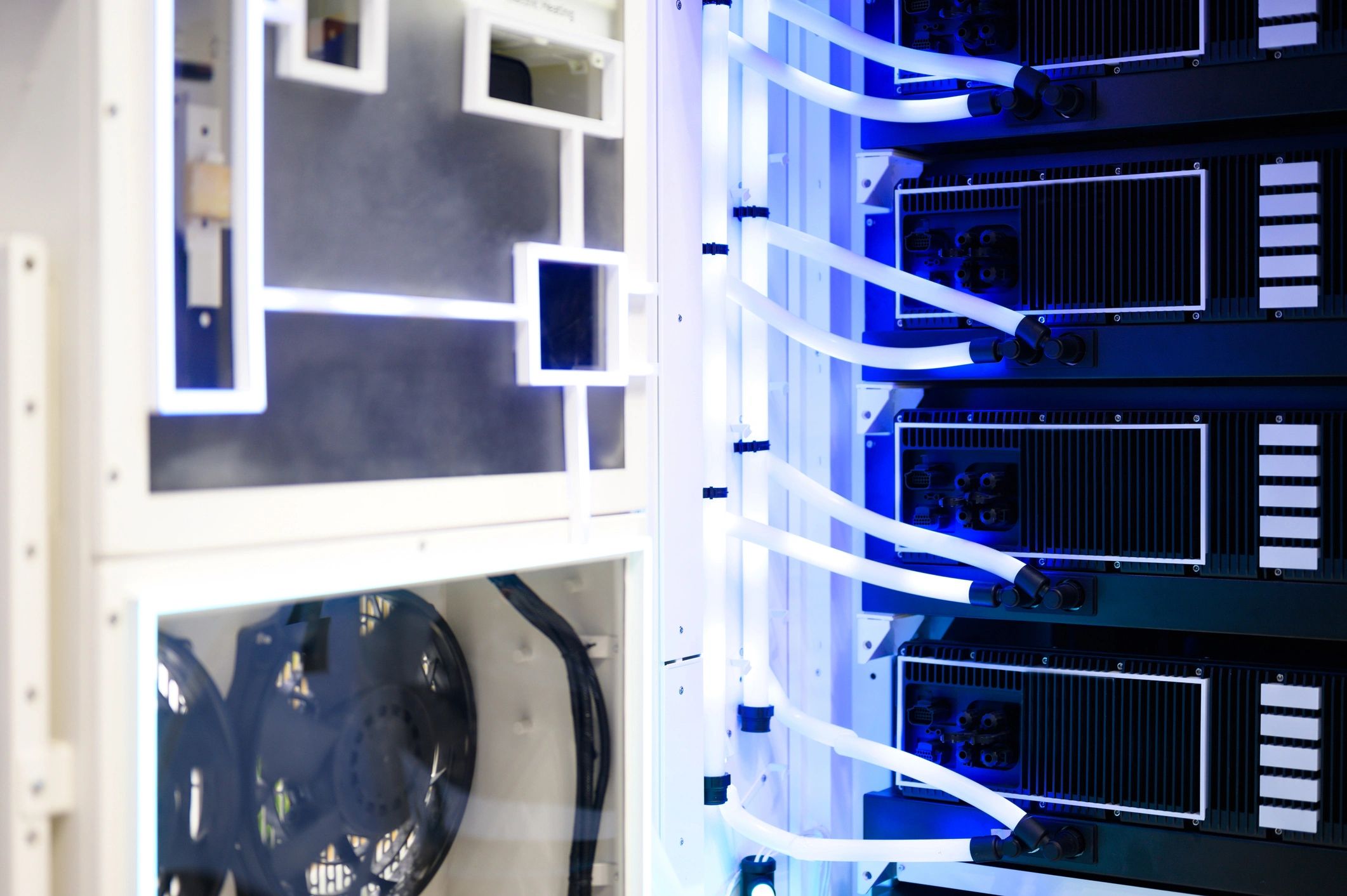
Ruggedization & hardening
Options for environmental protection, vibration/shock considerations, and enhanced enclosure/fit-out for demanding sites and transport profiles.

Rapid deployment
Prefabricated, tested modules with defined milestones—from design freeze to delivery, installation, and commissioning support.

Operational continuity
Resilient power and cooling approaches, maintainability, and service access designed to keep mission systems online.
What we deliver
Engineering-led support for secure programmes
Secure configuration & reference architecture
Define IT load, security posture, network zones, and operational constraints—then map to a Modular Data System configuration with clear assumptions.
Deployment planning & commissioning support
Structured delivery from discovery to build, transport, install, test and handover—aligned to your site access, timelines, and responsibilities.
Documentation for procurement & consultants
Spec packs, drawings, and compliance/security notes designed to accelerate evaluation and reduce back-and-forth.
Lifecycle serviceability & spares strategy
Maintainability-focused layouts, service access planning, and recommended spares/replaceable units to support uptime in remote locations.
Defence & secure FAQ
Direct answers to common evaluation questions. For programme-specific requirements, request a spec pack or book a technical call.
Can you support classified or restricted environments?
We can provide configurations and documentation aligned to secure operating models. Final accreditation and compliance decisions remain with your authority and programme requirements.
What security options are available?
Options can include enhanced physical security, access control integration, CCTV provisions, tamper-evident approaches, and network zoning-ready layouts.
How fast can a secure module be deployed?
Timelines depend on configuration and hardening level. We offer standard and fast-track paths with clear milestones from design freeze to delivery and commissioning support.
Do you provide drawings and technical submittals?
Yes—spec packs, reference architectures, and drawings are available to support consultants and procurement reviews.
Can modules be expanded over time?
Modular Data System is designed for scalable deployments—add capacity by deploying additional modules and aligning power/cooling/network interfaces.
How do we start a spec or quote process?
Share your IT load, target security posture, site constraints, and timeline. We’ll respond with a recommended configuration and next steps.

Next step
Get a secure configuration recommendation
Tell us your IT load, hardening level, site constraints, and deployment timeline. We’ll respond with a Modular Data System configuration, assumptions, and a clear path to procurement.